Get the CrowdStrike® 2021 Global Threat Report -- one of the industry’s most highly anticipated reports on today’s top cyber threats and adversaries.
Tuesday, 16 March 2021
Saturday, 13 March 2021
The Zero Trust Mindset
An excellent post about Zero Trust concept from Alex Weinert from Microsoft
Original Post: https://techcommunity.microsoft.com/t5/azure-active-directory-identity/zero-hype/ba-p/1061413
In a Nutshell
Zero Trust, conceptually, asserts that traditional security models based on “the walled garden” are outdated, and that security models should assume that all requests should be treated as though they originate from an uncontrolled (external or compromised) network. Whether you think of this as “assuming breach” and operating as though the enemy is inside your perimeter or you think of this as operating in a perimeter-less environment, it’s all about operating as though you are in a pervasive threat environment. This is a simple concept, we don’t need to complicate it or dress it up because it has powerful implications.
The Zero Trust Mindset
I believe the most useful thing about Zero Trust is the mindset it creates. The mindset to adopt is that you are operating in a pervasive threat environment. An environment that demands that you continuously assess and re-assess the viability of your security strategy. Here are some key behaviors you might exhibit if you accept that you are operating in a pervasive threat environment:
- Don’t accept complacency. This is the single biggest shift of Zero Trust. In the world of flat networks and VPN, we assume that if the request is originating from a known network, it must be safe. We assume the models that protected us yesterday will protect us tomorrow. Zero Trust demands we abandon those assumptions and instead validate and exercise controls over as many aspects of access as possible, explicitly validating what we can, and accepting that the things we don’t explicitly validate remain uncertain.
- Assume all resources are on the open internet. One approach many customers have found valuable in countering their entrenched assumptions is to assume every user, device, and resource is on the public internet. Many of our most successful customers in this regard have simply moved as many resources as possible to the cloud, modernizing their security strategy as they go.
- Trust no single source. In a pervasive threat environment, accurate insights are key. A CISO once shared that “Pops told me, honest people all tell the same story, but liars lie differently.” Security models which rely on multiple sources of validation are much stronger – triangulation provides a much more accurate fix than single source validation. Similarly, control which relies on multiple elements (using device trust, location, and strong auth, for example) is better than that which relies on only one aspect of access.
- Breach containment. If we assume pervasive threats, we assume that some threats will break through our defenses. Containment strategies such as privileged identity management, role-based access, separation of duties and network segmentation can help contain adversaries who break through your first layers of defense.
- Standards are security. While innovation is wonderful, a maxim of security (especially encryption) is that nothing is provably secure, but time without breach is a good indicator. Avoid security theater or security through obscurity – heavily inspected, heavily used, and yes - heavily attacked standards provide a great anchor for your security strategy. Leverage modern authentication standards like OAUTH2, provisioning standards like SCIM, and credential standards like FIDO2 wherever possible (or buy products that do).
- There aren’t enough humans. You must automate everything you possibly can. There simply aren’t enough humans to handle the volume of telemetry and attacks you will be facing. Make use of cloud intelligence, machine learning, and most importantly automated response mechanisms like automatically locking at risk accounts or banning traffic from known bad IP addresses.
We can distill all this down to three key principles:
- Move from assumption to explicit verification.
- Adopt a policy-based, least privileged access model.
- Design with the assumption that every element of your system can be breached.
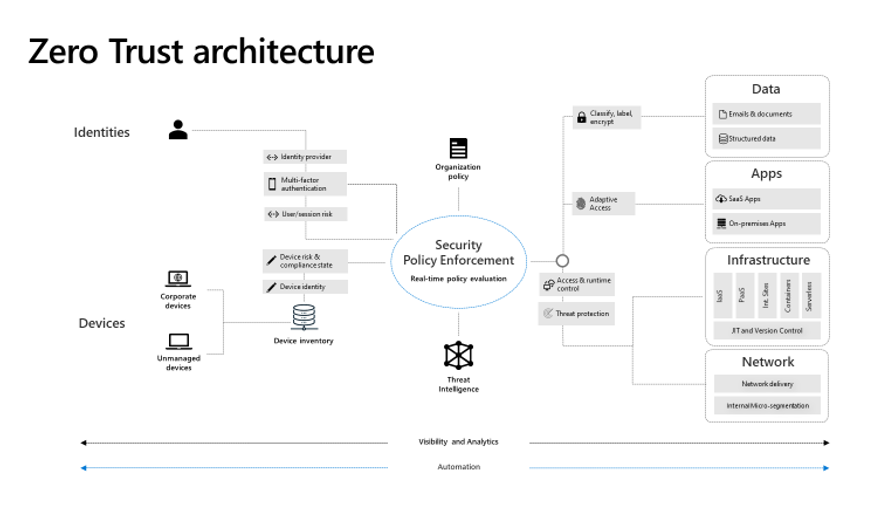
Conceptual Architecture
We have seen that successful adoption of a Zero Trust approach benefits from some critical elements. We pulled this together conceptually in a conceptual architecture, pictured below.
The critical elements are as follows. First, the key resources:
- Verify Identity. Knowing who is requesting access is essential, and that identity must be validated explicitly, not inferred from the environment. Ensure you are secure at the point of access by bringing users into a common identity system, using strong auth and threat intelligence to validate authentication.
- Verify Devices. All data access requests result in the transfer of that data to a browser or app on a device. Knowing the state of that device is critical in a world where devices can be infected, lost, or stolen. Mobile Device Management (MDM) and Mobile Application Management are critical to protecting data once it is accessed.
- Protect Data. Wherever possible, data should be protected from unauthorized transfer by auto-classification and encryption. This protects against intentional or accidental misrouting of downloaded data.
- Harden Applications. Application access and configuration must be secure to mitigate intrinsic application risks, and to ensure access is governed by policy. Application behavior, including shadow IT, should be understood and monitored for and protecting from anomalies.
- Protect Infrastructure. Where you are using cloud workloads (IaaS or PaaS), ensure you are utilizing your cloud fabric according to best security principles, utilizing the intelligence and protection provided.
- Govern Networks. Mitigate lateral movement by using an intelligent, adaptive segmentation strategy for workloads, monitoring for and protecting from anomalous traffic patterns.
Then, the key tools to tie it together:
- Policy driven access. Modern micro-segmentation means more than networks. It requires we also gate access based on their role, location, behavior patterns, data sensitivity, client application, and device security. Ensure all policy is automatically enforced at the time of access and continuously throughout the session where possible.
- Automated threat detection and response. Telemetry from the systems above must be processed and acted on automatically. Attacks happen at cloud speed – your defense systems must act at cloud speed as well, and humans just can’t react quickly enough. Integrate intelligence with policy-based response for real-time protection.
Next Steps
Here are some next steps and related on demand sessions to help you go deeper on how to get started today:
Identity Teams:
- Connect all your apps for single sign-on – Identity is your control plane, but only for apps and users that are visible to it!
- Ensure strong identity with multi-factor authentication and risk detection.
- Enforce policy-based access and least privileged access for breach containment.
- Check out these sessions:
Device Management Teams:
- Register your devices with your Identity provider so you can consider device context in your policies.
- Implement MDM security baselines with compliance reporting.
- Implement role-based access control that allows view access for impact assessment.
- Check out this session:
- DEP50: Why Microsoft 365 device management is essential to your Zero Trust strategy
Network and Infrastructure Teams:
- Enable a cloud workload protection solution across your hybrid and multi-cloud estate.
- Use cloud-native controls to create micro perimeters.
- Reduce attack surface by implementing just-in-time application and network segmentation.
- Check out these sessions:
Application and Data Teams:
- Perform shadow IT discovery and implement a cloud control program – you can’t manage what you can’t see.
- Agree on a label taxonomy and classify documents and emails – use default taxonomy for initial classifications.
- Apply protections to high risk scenarios such as sensitive data and unmanaged access in apps.
- Check out these sessions:
Finally, check out our Zero-Trust center and especially the maturity model which we hope will help you think about next steps on your journey.
Thursday, 7 April 2011
Microsoft Security Updates - April 2011
Operation b107 - Rustock Botnet Takedown - Using the knowledge gained during its takedown of the botnet Waledac just over a year ago, the Microsoft Digital Crimes Unit (DCU) has successfully taken down a larger, more notorious and complex botnet known as Rustock, which had an estimated infection count above one million computers and was capable of sending billions of spam messages per day. Learn more more on The Official Microsoft Blog
Earthquake in Japan- How to Help While Avoiding Donation Fraud - When we hear about a disaster like the earthquake in Japan, many of us try to think of ways we can help. Read this Security Tips & Talk blog post for valuable tips you can pass on to your end users to help them avoid online donation scams.
Microsoft Security Bulletin Summary for March, 2011
http://www.microsoft.com/technet/security/bulletin/ms11-mar.mspx
Security Bulletin Overview for March 2011
Microsoft Security Response Center (MSRC) Blog Post http://go.microsoft.com/?linkid=9683067
Forefront Security TechCenter - http://technet.microsoft.com/en-gb/forefront/default.aspx
Please note that if you have feedback on documentation or wish to request new documents - email isadocs@microsoft.com
Forefront Threat Management Gateway 2010 homepage
http://technet.microsoft.com/en-gb/forefront/ee807302.aspx
The ISA Server Product Team Blog (http://blogs.technet.com/isablog/) is updated on a regular basis. Latest entries include:
New WIKI Article by Yuri Diogenes–”Forefront TMG 2010 Survival Guide”
http://blogs.technet.com/b/isablog/archive/2011/02/27/new-wiki-article-by-yuri-diogenes-forefront-tmg-2010-survival-guide.aspx
Forefront Unified Access Gateway 2010 Technical Resources
http://technet.microsoft.com/en-gb/forefront/edgesecurity/ee907407.aspx
For comments, feedback, and requests, contact the Forefront UAG User Assistance team at uagdocs@microsoft.com.
Forefront Unified Access Gateway Product Team Blog
The UAG Product Team Blog (http://blogs.technet.com/edgeaccessblog) is updated on a regular basis. Latest entries include:
No place like HOD
http://blogs.technet.com/b/edgeaccessblog/archive/2011/03/15/no-place-like-hod.aspx
Security Tip of the Month- Improving Security Using Attack Surface Analyzer - Learn how to use Attack Surface Analyzer, a free tool from Microsoft, to better understand the aggregate attack surface change that may result from the introduction of line-of-business (LOB) applications to the Windows platform.
Microsoft Security Compliance Manager - The Microsoft Security Compliance Manager (SCM) will help you plan, deploy, operate, and manage your security baselines for the most widely used Microsoft technologies. Learn more about this free tool—which includes security baselines for Windows Server 2008 R2, Microsoft Office 2010, Windows 7, and Internet Explorer8—then check out tips for getting started and answers to answers to frequently asked questions.
Infrastructure Planning and Design Guide for Malware Response - Looking to limit the risk of malware infection? This new guide can help your organization determine the best and most cost-effective response strategy for malware outbreaks. Learn how your quick decisions can return systems to operation while limiting your exposure then download the guide.
Malicious Software Removal Tool - Need to check your computers for malware infection? Download the Microsoft Windows Malicious Software Removal Tool. Updated monthly and available in x86 and x64 versions, the tool checks Windows Vista, Windows 7, Windows XP, Windows 2000, and Windows Server 2003 computers for, and helps remove, infections by specific, prevalent malicious software-including Blaster, Sasser, and Mydoom. When the detection and removal process is complete, the tool displays a report describing the outcome including which, if any, malicious software was detected and removed.
Getting Started with the SDL Threat Modeling Tool - Find tips to help you get started with the Microsoft Security Development Lifecycle (SDL) threat modeling approach and learn how to use the tool to develop great threat models as a backbone of your security process. Available as a free download, the SDL SDL Threat Modeling Tool helps engineers analyze the security of their systems to find and address design issues early in the software lifecycle.
Microsoft Baseline Security Analyzer- Frequently Asked Questions - Get answers to frequently asked questions about Microsoft Baseline Security Analyzer (MBSA) 2.2 including system requirements, configuration, scanning, and reporting. MBSA 2.2 provides a streamlined method for IT pros to identify missing security updates and common security misconfigurations.
Detecting Security Bulletins with the Extended Security Update Inventory Tool - The Extended Security Update Inventory Tool is designed to help IT pros identify Microsoft Systems Management Server (SMS) client computers that may need security updates that are not detectable using the existing SMS Security Update Inventory Tool built on MBSA.
Downloads
Keeping Enterprise Data Safe with Office 2010
Keeping Enterprise Data Safe with Office 2010 - Office 2010 Security Whitepaper
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=4a9e2382-f375-43bf-b5d6-dcf9df5c3e37
Business Intelligence Competency Center (BICC) Core System Documentation: Encoding and Unicode Considerations
Describes what you need to know when dealing with Encoding and Unicode in applications built on top of Microsoft solutions.
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=4b8c3058-0821-492a-ad3d-5e8ad9a5e9d1
Microsoft Forefront Online Protection for Exchange Service Level Agreement (SLA)
This document has been moved. Please update your links and bookmarks with the new location, listed below.
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=f5714ed7-f14d-499e-b7d9-3365c9008113
NTFS Chkdsk Best Practices and Performance
This document provides best practices for using NTFS Chkdsk.
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=35a658cb-5dc7-4c46-b54c-8f3089ac097a
QFE Rollup Package 2 for System Center Data Protection Manager 2010
This download fixes issues in Microsoft System Center Data Protection Manager (DPM) 2010
Please read KB article 2465832 for complete information.
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=d3fabb18-1adb-4c87-a95d-d3c3826d5bfb
Microsoft Exchange Hosted Archive Service Level Agreement (SLA)
This document has been moved. Please update your links and bookmarks with the new location, listed below.
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=01c1168f-8f59-4746-9b42-f1166bb7142d
AD CS Step-By-Step Guide
This document describes the steps needed to set up a basic public key infrastructure.
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=44315bff-b744-4637-a66b-e69b4955ee45
Update for Windows Mail Junk E-mail Filter [March 2011] (KB905866)
Install this update for Windows Mail to revise the definition files that are used to detect e-mail messages that should be considered junk e-mail or that may contain phishing content.
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=aa029fde-f341-44fc-8b85-0c6f3d3c2d69
Microsoft® Windows® Malicious Software Removal Tool (KB890830)
This tool checks your computer for infection by specific, prevalent malicious software (including Blaster, Sasser, and Mydoom) and helps to remove the infection if it is found. Microsoft will release an updated version of this tool on the second Tuesday of each month.
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=ad724ae0-e72d-4f54-9ab3-75b8eb148356
Microsoft® Windows® Malicious Software Removal Tool (KB890830) x64
This tool checks your computer for infection by specific, prevalent malicious software (including Blaster, Sasser, and Mydoom) and helps to remove the infection if it is found. Microsoft will release an updated version of this tool on the second Tuesday of each month.
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=585d2bde-367f-495e-94e7-6349f4effc74
March 2011 Security Release ISO Image
This DVD5 ISO image file contains the security updates for Windows released on Windows Update on March 11th, 2011.
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=ab55654c-c685-4316-93fc-e3a80cccac71
Suite B PKI in Windows Server 2008
This document provides guidance for the planning and implementation of a Microsoft Windows Server 2008 and Windows Server 2008 R2 public key infrastructure (PKI) using Suite B compliant cryptographic algorithms
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=6f319ffa-739e-4fe8-bac3-92547baef7a9
Cross-forest Certificate Enrollment with Windows Server 2008 R2.doc
This paper explains how cross-forest certificate enrollment works. It also provides deployment guidance for cross-forest certificate enrollment in new and existing Active Directory Certificate Services (AD CS) deployments.
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=d408be72-7c74-4b19-a2de-fa11858c30b2
Configuring and Troubleshooting Certification Authority Clustering in Windows Server 2008 and Windows Server 2008 R2
This guide describes how to install, configure, and troubleshoot failover clustering with Active Directory Certificate Services in Windows Server 2008 and Windows Server 2008 R2.
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=15c75333-be26-4955-a32c-03077daf1631
Certificate Enrollment Web Services in Windows Server 2008 R2
This paper explains how certificate enrollment Web services work in Windows Server 2008 R2. It also provides deployment guidance for certificate enrollment Web services in new and existing Active Directory Certificate Services (AD CS) deployments.
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=28b910f8-6374-48dd-a897-11fff62ab795
Active Directory Certificate Services (AD CS)
This download center location contains information related to administering Active Directory Certificate Services (AD CS)
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=d9cbaab9-552b-45f0-a8ac-b3cb4009f068
Microsoft SCEP Implementation Whitepaper.
This whitepaper provides an overview of Microsoft implementation for SCEP in the Windows Server 2008 R2
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=e11780de-819f-40d7-8b8e-10845bc8d446
Active Directory Certificate Services Upgrade and Migration Guidance
This document discusses the planning and implementation of a Windows Server 2008 Active Directory Certificate Services (AD CS) upgrade and migration from an existing Windows public key infrastructure (PKI), including scenarios and step-by-step instruction.
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=c70bd7cd-9f03-484b-8c4b-279bc29a3413
Webapps_Webcast_series_Jan_2011_videos
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=a33b795b-f529-4a20-9335-ae2281e756cf
Microsoft IT CISO Perspective on Cloud Security
In this session, you will hear directly from Microsoft’s CISO as he shares his perspective on cloud security.
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=d48897ce-e0f5-4bde-a480-c1d6378578b8
Microsoft Forefront Endpoint Protection 2012 Privacy Statement
Microsoft Forefront Endpoint Protection 2012 Privacy Statement
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=e72065f9-c08d-4c50-b785-b98416b530e3
SharePoint Server 2010 site and content security worksheet
Use this worksheet to record inherited and unique permissions, and record which groups need what level of access.
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=478a6cdf-8b3c-4b2e-993f-be07715466a6
SharePoint Foundation 2010 site and content security worksheet
Use this worksheet to record inherited and unique permissions, and record which groups need what level of access.
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=3ce0858d-0d59-4f70-8a55-1e493ea7c742
Events/WebCasts
Security Webcast Calendar http://go.microsoft.com/fwlink/?LinkId=37910
Find security webcasts listed in an easy-to-use calendar format.
Upcoming Security Webcasts
http://www.microsoft.com/events/security/upcoming.mspx
MSDN Webcast: Security Talk: Using the Attack Surface Analyzer (Level 200)
Thursday, April 07, 2011 1:00 P.M.-2:00 P.M. Pacific Time
TechNet Webcast: Information About Microsoft April Security Bulletins (Level 200)
Wednesday, April 13, 2011 11:00 A.M.-12:00 P.M. Pacific Time
On-Demand Security Webcasts
http://www.microsoft.com/events/security/ondemand.mspx
News
Windows Internet Explorer 9 Released to Web
You can now download Internet Explorer 9. Check out the latest features for IT professionals, and get guidance to help you pilot and deploy this enterprise-ready browser in your organization with the Springboard Series for Internet Explorer 9.
http://windows.microsoft.com/en-US/internet-explorer/products/ie/home
http://technet.microsoft.com/en-us/ie/default
Visual Studio 2010 Service Pack 1 now available
Visual Studio 2010 Service Pack 1 includes a host of improvements and fixes based on your feedback, including a local Help Viewer, Silverlight performance tuning, .NET 3.5 unit testing, IntelliTrace for 64-bit and SharePoint, and much, much more.
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=75568aa6-8107-475d-948a-ef22627e57a5&displaylang=en
Microsoft App-V 4.6 Service Pack 1 and MED-V 2.0 Released
Microsoft Desktop Optimization Pack (MDOP) 2011, featuring Microsoft App-V 4.6 Service Pack 1 (SP1) and MED-V 2.0, is now available. App-V 4.6 SP1 makes App-V packaging easy, fast, and predictable, and MED-V 2.0 is easier to use than ever, with no dedicated infrastructure required
http://blogs.technet.com/b/mdop/archive/2011/03/09/app-v-4-6-sp1-and-med-v-2-0-are-available-as-part-of-mdop-2011.aspx
Windows Virtualization Team Blog - http://blogs.technet.com/virtualization
The World Simplified is a Virtual World - http://blogs.technet.com/virtualworld
The App-V Product Team Blog - http://blogs.technet.com/appv
The Official MDOP Blog - http://blogs.technet.com/mdop
Ask the Directory Services Team - http://blogs.technet.com/askds
Ask the Performance Team - http://blogs.technet.com/askperf
Microsoft Enterprise Networking Team - http://blogs.technet.com/networking
Ask the Core Team - http://blogs.technet.com/askcore
Ntdebugging Blog - http://blogs.msdn.com/ntdebugging
The Hot Blog - http://blogs.technet.com/hot
TRM - http://blogs.technet.com/trm/default.aspx
Downloads
Windows Internet Explorer 9 Released to Web
You can now download Internet Explorer 9. Check out the latest features for IT professionals, and get guidance to help you pilot and deploy this enterprise-ready browser in your organization with the Springboard Series for Internet Explorer 9.
http://windows.microsoft.com/en-US/internet-explorer/products/ie/home
http://technet.microsoft.com/en-us/ie/default
Group Policy Settings Reference Windows Internet Explorer 9
This spreadsheet lists the policy settings for computer and user configurations included in the administrative template files (admx/adml) delivered with Windows Internet Explorer 9.
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=21e84c24-b967-4d6d-850a-5eb554d18447
Visual Studio 2010 Service Pack 1 now available
Visual Studio 2010 Service Pack 1 includes a host of improvements and fixes based on your feedback, including a local Help Viewer, Silverlight performance tuning, .NET 3.5 unit testing, IntelliTrace for 64-bit and SharePoint, and much, much more.
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=75568aa6-8107-475d-948a-ef22627e57a5&displaylang=en
VMM 2012 Beta Eval (VHD)
System Center Virtual Machine Manager 2012 delivers industry leading fabric managment, virtual machine management and services deployment in private cloud environments.
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=76002803-4fe8-4573-a76d-6b2b11adfe58
System Center Virtual Machine Manager (VMM) 2012 Beta Documentation
This download provides technical documentation for the Beta release of VMM 2012.
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=f7c174f2-1d39-4fed-9778-3f41b84f744b
Server App-V Beta Documentation
The beta documentation for Microsoft Server Application Virtualization (Server App-V) is available in this download.
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=d24bbf9b-9d9c-4966-90e5-575852c9258b
Microsoft Windows Server 2008 Hyper-V Common Criteria Guide
This is the supplemental administrator guidance documentation that was used in the Common Criteria evaluation of Microsoft Windows Server 2008 Hyper-V.
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=cb19538d-9e13-4ab6-af38-8f48abfdad08
System Center Virtual Machine Manager 2008 R2 Service Pack 1 – Evaluation
System Center Virtual Machine Manager 2008 R2 SP1 (VMM) is a comprehensive management solution for the virtualized data center. It enables increased physical server utilization, centralized management of virtual machine infrastructure, and rapid provisioning of new virtual machines by the administrator, delegated administrator, and authorized end users.
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=9189bbce-d970-4c6c-9dd3-9e65798ecd70
BranchCache Learning Roadmap
This learning roadmap provides you with links to prerequisite information you need to understand and deploy BranchCache, and also provides links to BranchCache information from level 100 to level 300. In addition there are links to optional information that will enhance your ability to expand and manage your BranchCache deployment.
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=cda652cf-c954-4b78-9e1b-7a660dc3b867
Microsoft Desktop Virtualization Data Sheets
Learn how Microsoft Desktop Virtualization Solutions can empower organizations to provide employees with the flexibility to work everywhere on a range of devices, while simplifying compliance and business continuity through a centralized and unified management infrastructure.
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=81d1d1b8-e0e2-43c1-be91-6a5382f8ac39
Managing Microsoft Desktop Virtualization
Learn about managing desktop virtualization solutions with Microsoft technologies..
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=59e220ee-e7a1-4f8e-a86a-538b854c5e18
Microsoft RemoteFX for Remote Desktop Virtualization Host Capacity Planning Guide for Windows Server 2008 R2 Service Pack 1
This white paper is intended as a guide for capacity planning of Microsoft RemoteFX in Windows Server 2008 R2 Service Pack 1.
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=679193cb-9b74-4590-a2be-00bde429c990
Remote Desktop Session Host Capacity Planning in Windows Server 2008 R2 and Microsoft RemoteFX in Windows Server 2008 R2 with Service Pack 1
This white paper is intended as a guide for capacity planning of RD Session Host in Windows Server 2008 R2 and RemoteFX in Windows Server 2008 R2 with Service Pack 1 (SP1).
http://www.microsoft.com/downloads/en/details.aspx?FamilyID=ca837962-4128-4680-b1c0-ad0985939063
Events/Webcasts
Full list can be found at: http://www.microsoft.com/events/default.mspx
Interactive Webcast Calendar
The interactive calendar will help you quickly find live webcasts that fit your schedule as well as on-demand webcasts to view at your convenience. You can choose your time zone and filter this list by audience, webcast series, product or topic, and presenter.
http://www.microsoft.com/events/webcasts/calendar/monthview.aspx
Monthly Archived Webcasts:
http://www.microsoft.com/events/webcasts/library/default.mspx
April WebCast Calendar
http://www.microsoft.com/events/webcasts/calendar/MonthView.aspx?stdate=4/1/2011&audience=0&series=0&product=0&presenter=0&tz=0
New KB's
Problems with Windows 7 parsing MCCS information - http://support.microsoft.com/kb/2515532
“Access Denied” error trying to rename a file on share available offline -
http://support.microsoft.com/kb/2457622
Event ID 7000 or 7026 may be logged in the System log on a computer that is running Windows 7, Windows Vista, Windows Server 2008 R2, or Windows Server 2008 - http://support.microsoft.com/kb/933757
Error message when installing RSAT: 'This update is not applicable to your computer' - http://support.microsoft.com/kb/2517239
Display Changes Resolution on Windows 7 While Pressing Win+P Hot Key and Select Duplicate When Only One Monitor is Connected -
http://support.microsoft.com/kb/2518084
The GetGlyphOutline() function incorrectly returns glyphs from the GulimChe font in Windows 7 - http://support.microsoft.com/kb/2447659
A DNS Update is recorded as failed: Event ID 5774, 1196, or 1578 - http://support.microsoft.com/kb/977158
Windows 7 stops responding when you print to a Bluetooth printer - http://support.microsoft.com/kb/2461648
[SDP 3][506d1864-dc2a-493c-be61-defc84fbcd60] Volume License Activation - Windows 7 and Windows Server 2008 R2 - http://support.microsoft.com/kb/2518799
[SDP 3][10678477-8f52-4968-8848-01305cbcc3c1] Performance - Windows 7 and Server 2008 R2 - http://support.microsoft.com/kb/2516512
Microsoft inbox DSM may not perform well on system with many processors - http://support.microsoft.com/kb/2517251
Using Hyper-V with large sector drives on Windows Server 2008 and Windows Server 2008 R2 - http://support.microsoft.com/kb/2515143
Remote Desktop or RemoteApp session does not terminate due to spawned splwow64.exe process - http://support.microsoft.com/kb/2513330
Physical Memory Limits in Crash Dump files for Windows 7 and Windows 2008 R2 - http://support.microsoft.com/kb/2510168
Group Policy Editor incorrectly displays value for drop-down box data in Group Policy settings if opened maximized - http://support.microsoft.com/kb/2494205
The DNS Zone Transfer setting is not retained in Windows Server 2008 - http://support.microsoft.com/kb/2514953
You cannot manage a remote DNS server by using RSAT or the DNS MMC on Window Server-based computers - http://support.microsoft.com/kb/2514936
A static record is not updated to a dynamic record as expected in the Windows Server MMC - http://support.microsoft.com/kb/2514994
Directory Services - Windows 7 and Server 2008 R2 - http://support.microsoft.com/kb/2515358
A hotfix is available to update the Daylight Saving Time for Chile for Windows Operating Systems - http://support.microsoft.com/kb/2519231
MS11-015: Description of the security update for Windows XP Media Center Edition 2005: March 8, 2011 - http://support.microsoft.com/kb/2502898
MS11-017: Description of the security update for Remote Desktop client 5.2: March 8, 2011 - http://support.microsoft.com/kb/2483618
Offline File Synchronization – In Windows 7 the "Work Offline/Work Online" option button disappears from Windows Explorer after an offline / online transition and the Client Side Cache remains offline until the next restart of the computer - http://support.microsoft.com/kb/2512089
A device may be displayed as the default icon on the network map when the network has more than 10 hosts - http://support.microsoft.com/kb/2506718
Keys in the CNG user interface are always described as having no description in Windows 7 or in Windows Server 2008 R2 - http://support.microsoft.com/kb/2507840
A black screen is displayed when a Windows 7 SP1-based or Windows Server 2008 R2 SP1-based computer tries to enter hibernation - http://support.microsoft.com/kb/2496744
MS11-017: Vulnerability in Remote Desktop client could allow remote code execution: March 8, 2011 - http://support.microsoft.com/kb/2508062
MS11-017: Description of the security update for Remote Desktop client 7.0: March 8, 2011 - http://support.microsoft.com/kb/2483614
Saturday, 18 December 2010
Microsoft Security updates for December
Our top 10 security stories of 2010
What computer security topics do our readers care about most? Take a look at our most popular articles and blog posts from the past year.
- Download free antivirus and antispyware software
- Safer surfing with SmartScreen filter
- How to recognize phishing email messages and links
- Avoid scams that use the Microsoft name fraudulently
- Microsoft Security Essentials vs. Windows Defender
- Hey! Did MSN hijack my browser?
- Watch out for fake virus alerts
- "I've been mugged. Send money!"
- Got a virus? Get free help fast
- Speed up your PC
| ||
| ||
| ||
| ||
| ||
|
Saturday, 13 November 2010
The fight against botnets: Are we winning?
| |||||||
| |||||||
| |||||||
| |||||||
| |||||||
|
Tuesday, 12 October 2010
Security Articles from MS this month
Security
Microsoft Malware Protection Center Website | RSS Feed
Prehistoric Virtual Machines - 08-Oct-2010
Microsoft Security Response Center MSRC Website | RSS Feed
Advance Notification Service for October 2010 Security Bulletin - 07-Oct-2010
Security Bulletins Comprehensive Website | RSS Feed
Microsoft Security Bulletin Advance Notification for October 2010 - 07-Oct-2010
Security Products Forefront
Forefront Product Suite Website | RSS Feed
Microsoft acquires AVIcode Inc. to extend application management to the cloud - 07-Oct-2010
Forefront Server Security Website | RSS Feed
Hotfix rollup 3 for Forefront Security for Exchange Server SP2 and hotfix rollup 3 for Forefront Security for SharePoint SP3 are now available - 08-Oct-2010
Forefront Threat Management Gateway ISA Server Website | RSS Feed
TMG Reports stop working after installing TMG 2010 SP1 - 05-Oct-2010