Friday, 18 June 2021
Anatomy of a Supply Chain Attack
Ref: https://securityaffairs.co/wordpress/119051/cyber-crime/unc2465-supply-chain-attack.html
Tuesday, 15 June 2021
Friday, 28 May 2021
Recommendations to minimize Lateral Movement
Lateral Movement consists of techniques that adversaries use to enter and control remote systems on a network. Following through on their primary objective often requires exploring the network to find their target and subsequently gaining access to it. Reaching their objective often involves pivoting through multiple systems and accounts to gain. Adversaries might install their own remote access tools to accomplish Lateral Movement or use legitimate credentials with native network and operating system tools, which may be stealthier.
Lateral Movement Techniques
- Exploitation of Remote Services
- Internal Spearphishing
- Lateral Tool Transfer
- Remote Service Session Hijacking
- SSH Hijacking
- RDP Hijacking
- Remote Services
- Remote Desktop Protocol
- SMB/Windows Admin Shares
- Distributed Component Object Model
- SSH
- VNC
- Windows Remote Management
- Replication Through Removable Media
- Software Deployment Tools
- Taint Shared Content
- Use Alternate Authentication Material
- Application Access Token
- Pass the Hash
- Pass the Ticket
- Web Session Cookie
- Use Standard User Accounts: Enforce that all users have a standard user account. Administrators across all platforms should log in with their standard accounts as normal practice. They should only log in with administrative rights when they need to perform administrative tasks. Sounds reasonable. Doesn’t always happen.
- Enforce the Principle of Least Privilege: If a user does not need access to systems, applications or data, remove it. As a first step remove administrator rights on desktops for all users.
- Implement Application Allow listing: Implement policy to allow known good applications and log all other applications and launch attempts. If possible, restrict launching of end user applications with known critical security vulnerabilities.
- Implement Multifactor Authentication: Implement multi-factor authentication for access to internal systems, applications and even data. While implementing static multi-factor based on whether a system or application is good, getting too restrictive can become frustrating for users. Look for solutions that can also restrict access based on the risk associated with the environment or activity. For example, if someone tries to launch a sensitive application after hours for the first time, or tries to run a sensitive command on the Unix server that is missing critical patches, step up the security and trigger to re-authenticate with multi-factor.
Note: SMB can provide a convenient MFA bypass for adversaries, handing them a foothold that will allow for remote code execution without any additional authentication factor. Depending on the environment, SMB may also provide adversaries the ability to disable security controls (including MFA) and improve their position in the network.
In many environments that implement MFA using 3rd party provider, an attacker may remove the MFA restriction with their SMB-based shell. They achieve this by enabling ‘Restricted Admin Mode’. This seems counterintuitive, but works for many MFA clients because restricted admin mode changes the supported Windows logon types and takes the MFA provider out of the picture. The setting is controlled via a single registry key: “HKLM\System\CurrentControlSet\Control\Lsa\DisableRestrictedAdmin” and setting it to 0 is all that is required in many cases. This single change gives the adversary the option of single-factor RDP access to machines that would have otherwise been protected with an MFA prompt.You need to enable the Windows firewall in all profiles (domain, private, public) in the Servers and configure it to block inbound traffic by default. Through a simple Windows Firewall rule, distributed via Group Policy and applied to the workstations OU, all inbound communication on ports 139 and 445 could be denied by default. Further,
- Deny all SMB communication between workstations
- Deny most SMB communication from workstations to servers (wherever not required)
This would ensure -
- Lateral movement with SMB between workstations would be unlikely
- Malware which spreads via SMB is also unlikely to move through the workstations
- Use Context-Based and Adaptive Access Controls: At some point people need access to do their jobs, but continue to lock down when they have access, and from which location they have access. Restricting access based on static elements like time of day or subnet is good, but restricting access dynamically based on risk (i.e. does a ticket exist for the access, does this request adhere to a normal access patterns, have I received recent alerts from my threat detection layers, etc.) adds greater protections.
- Implement mitigations against Mimikatz: When Mimikatz first came out, Microsoft patched against that first version of code using KBKB2871997 (for Windows 7 era hosts, way back in 2014). https://support.microsoft.com/en-us/help/2871997/microsoft-security-advisory-update-to-improve-credentials-protection-a
Since then, this protection has been integrated into Windows 8.x, Windows 10 and Server 2016+. However, what you'll find is that these protections only protect against the initial vector. Mimikatz and Microsoft are in an ongoing game of "cat and mouse" over this issue, and newer versions of Mimikatz have newer attacks.
Mimikatz Specific Defenses -
- Update Active Directory's Functional level. Many of the Enterprise Protections aren't available unless the AD Functional Level is set to some modern version (Windows 2016)
- Disable the debug right for local administrators on all servers and workstation. To disable this setting in Group Policy, navigate to Security Settings / Local Policies / User Rights Assignments / Debug Programs.
By default, this is not configured - enable it, and don't add any users or groups to it (or add only the group(s) that truly need it)
- Disable the WDigest protocol across the board. It's disabled by default in Windows 8 and newer.
- Enable LSA protection (RunAsPPL registry key). This provides some protection of the memory used by the LSASS process. To enable this, in the registry, navigate to HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\LSA and set "RunAsPPL" to "1"
Note: This one does have some risk, as it tries to apply protections to other components that LSASS might call (like 3rd party authentication code). This is the first mitigation that carries risk - this can break things! Fortunately Microsoft has some audit settings that can be deployed in advance to assess if you have a problem in this area first. More details on this, and the setting in general can be found here: https://docs.microsoft.com/en-us/windows-server/security/credentials-protection-and-management/configuring-additional-lsa-protection
- Disable storage of plain text passwords in AD. To disable this, in Group Policy navigate to: Computer Configuration / Security Settings / Account Policies / Password Policy, and set "Store Passwords using reversible encryption" to "Disabled":
- Enable Restricted Admin Mode (“DisableRestrictedAdmin” and “DisableRestrictedAdminOutboundCreds” registry keys). This sets up your RDP session to NOT store credentials in the memory of the target host. To start a session in Restricted Admin Mode, run your RDP session as:
mstsc /restrictedadmin /v:targethost
You can also control this behaviour with registry keys:
In HKEY_LOCAL_MACHINE\System\CurrentControlSet\Control\Lsa, set the DWORD value DisableRestrictedAdmin to "0" to enable restricted mode (this setting does not exist by default)alsoHKEY_LOCAL_MACHINE\System\CurrentControlSet\Control\Lsa, the DWORD value to create and set is DisableRestrictedAdminOutboundCreds:Default value = doesn’t exist = 0 = Admin Outbound Creds are enabledValue =1 == Admin Outbound Creds are disabledMore can be found on these settings here: https://blogs.technet.microsoft.com/kfalde/2015/01/10/restricted-admin-mode-for-rdp-in-windows-7-2008-r2/
- Enforce “Enable Restrict delegation of credentials to remote servers” via group policy. This sets "restricted admin mode" as the default for all RDP sessions that are initiated by domain members that are in scope for that GPO. The GPO seeting is:
Computer Configurations > Policies > Administrative Templates > System > Credential Delegation, Then Set Restrict Delegation of credential to remote servers to "Enable" and "Require Restricted Admin"
- Enforce NLA (Network Level Authentication) for RDP sessions. To enforce this in Group Policy:
For Servers:Computer Configuration/Policies/Administrative Templates/ Windows Components/Remote Desktop Services/Remote Desktop Session Host/SecurityEnable: Require user authentication for remote connections by using Network Level Authentication
For Clients:Computer Configuration/Policies/Administrative Templates/Windows Components/Remote Desktop Services/Remote Desktop Connection ClientEnable: Configure server authentication for client and in the drop-down menu choose “Do not connect if authentication fails”
- Disable password caching. By default Windows will cache the last "x" number of authentications (including the password hashes), in case no Domain Controllers are available. You can disable this in Group Policy at:
Computer Configuration -> Windows Settings -> Local Policy -> Security Options -> Interactive Logon: Number of previous logons to cache -> 0Note: This might mess things up for people with laptops, who will want to login while away from the office. You can set up your VPN client to force a VPN connection before login, but that'll still cause you headaches if you need to authenticate to a wireless hotspot first. Often that is mitigated by telling people to allow tethering to their cellphone, and then in written policies and technical controls forbid the use of free/public hotspots such as hotel or coffee shop wifi. This is a simple and effective mitigation, but it needs some thought and communication in advance to make it work in many organizations. Please ONLY use this option if you could beforehand socialize the problems and solutions with laptop users in advance.
- Restrict Service or other Purpose-created Admin accounts to specific stations or servers. This one doesn't stop Mimikatz from stealing credentials from the machine, but what it does do is prevent the re-use of those credentials for lateral movement to other targets, which is usually the whole point of the attack.
- Implement Strong Password Policy Management: Require strong passwords, and that they should be changed frequently. Deny password reuse. Log failed authentication requests.
- Automate Password Management: Require unique passwords across all privileged systems and accounts. Eliminate hard coded passwords in service accounts and scripts. Implement SSH key management tools.
- Segment Networks: Group assets, including application and resource servers, into logical units that do not trust one another. Segmenting the network reduces the “line of sight” access attackers must have into your internal systems. For access that needs to cross the trust zones, require a secured jump server with multi-factor authentication, adaptive access authorization, and session monitoring.
- Consider Micro-Segmentation: Where possible, go beyond standard network segmentation. Segment based on context of the user, role, application and data being requested.
- Implement Threat and Advanced Behavior Monitoring: Somewhere along the line accounts have access to stuff. Implement base security event monitoring and advanced threat detection (including user behavior monitoring) to more accurately and quickly detect compromised account activity as well as insider privilege misuse and abuse.
Sunday, 23 May 2021
Sunday, 2 May 2021
Compromise of MS Exchange Server - MITRE ATT&CK Framework
- On March 2, 2021, Microsoft released out-of-band security updates to address vulnerabilities affecting Microsoft Exchange Server products.
- On March 3, 2021, after CISA and partners observed active exploitation of vulnerabilities, CISA issued Emergency Directive 21-02: Mitigate Microsoft Exchange On-Premises Product Vulnerabilities and Alert AA21-062A: Mitigate Microsoft Exchange Server Vulnerabilities.
- On March 31, 2021, CISA issued ED 21-02 Supplemental Direction V1, which directs federal departments and agencies to run newly developed tools—Microsoft’s Test-ProxyLogon.ps1 scriptand Safety Scanner MSERTto investigate whether their Microsoft Exchange Servers have been compromised.
- On April 13, 2021, CISA issued ED 21-02 Supplemental Direction V2, which directs federal departments and agencies to apply Microsoft's April 2021 Security Updatethat newly discloses and mitigates significant vulnerabilities affecting on-premises Exchange Server 2013, 2016, and 2019.
Saturday, 24 April 2021
Saturday, 10 April 2021
Wednesday, 7 April 2021
LinkedIn Fake Jobs for Spear Phishing
Since the COVID pandemic, unemployment rates have risen dramatically. It is a perfect time to take advantage of job seekers who are desperate to find employment. Thus, a customized job lure is even more enticing during these troubled times.
Hence, targeting such unsuspecting people to carry out Spear Phishing attacks on LinkedIn with fake job offers to infect them with a sophisticated BACKDOOR TROJAN - MORE_EGGS is the latest modus operendi.
Crafting the fake job offer based on the the target’s job position from LinkedIn increases the odds that the recipient will successfully detonate the malware. To increase the odds of success, the phishing lures take advantage of malicious ZIP archive files that have the same name as that of the victims' job titles taken from their LinkedIn profiles.For example, if the LinkedIn member's job is listed as Senior Account Executive—International Freight the malicious zip file would be titled Senior Account Executive—International Freight position (note the 'position' added to the end), cybersecurity firm eSentire's Threat Response Unit (TRU) said in an analysis. Upon opening the fake job offer, the victim unwittingly initiates the stealthy installation of the fileless backdoor, more_eggs. It uses normal Windows processes to run so it is not going to typically be picked up by anti-virus and automated security solutions so it is quite stealthy.
The below three elements make more_eggs, and the cybercriminals which use this backdoor very lethal -
Once installed, more_eggs maintains a stealthy profile by hijacking legitimate Windows processes while presenting the decoy "employment application" document to distract targets from ongoing background tasks triggered by the malware. Furthermore, it can act as a conduit to retrieve additional payloads from an attacker-controlled server, such as banking trojans, ransomware, credential stealers, and even use the backdoor as a foothold in the victim's network so as to exfiltrate data.
Reference links:
https://thehackernews.com/2021/04/hackers-targeting-professionals-with.html
Sunday, 4 April 2021
Automating threat actor tracking

The model enriches targeted attack notifications with additional context on the threat, the likely attacker and their motivation, the steps the said attacker is likely to make next, and the immediate action the customer can take to contain and remediate the attack. Below we discuss an incident in which automated threat actor tracking translated to real-world protection against a human-operated ransomware attack.
Read the full article by Microsoft 365 Defender Research Team - https://www.microsoft.com/security/blog/2021/04/01/automating-threat-actor-tracking-understanding-attacker-behavior-for-intelligence-and-contextual-alerting/
Saturday, 3 April 2021
Tuesday, 16 March 2021
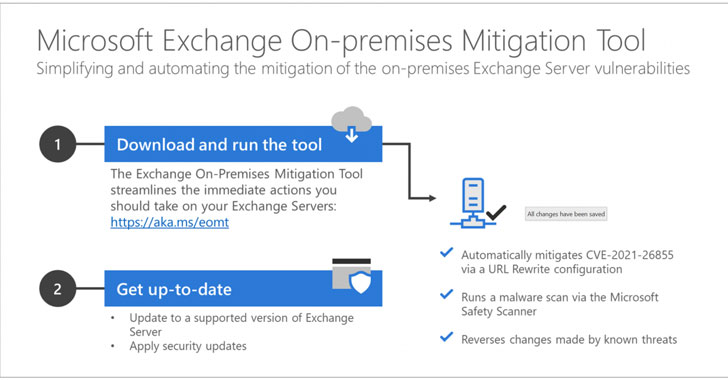
Exchange On-prem Mitigation Tool For ProxyLogon Exchange Server Cyberattacks
Microsoft on Monday released a one-click mitigation software that applies all the necessary countermeasures to secure vulnerable environments against the ongoing widespread ProxyLogon Exchange Server cyberattacks.
Called Exchange On-premises Mitigation Tool (EOMT), the PowerShell-based script serves to mitigate against current known attacks using CVE-2021-26855, scan the Exchange Server using the Microsoft Safety Scanner for any deployed web shells, and attempt to remediate the detected compromises.
"This new tool is designed as an interim mitigation for customers who are unfamiliar with the patch/update process or who have not yet applied the on-premises Exchange security update," Microsoft said.
Detailed info: https://thehackernews.com/2021/03/use-this-one-click-mitigation-tool-from.html