- Part 1: Ransomware Prevention Best Practices
- Part 2: Ransomware Response Checklist
Provided below are some of the predictions for 2021 by Forrester.
In 2021, Remote Work will rise to 300% of pre-COVID levels
Most companies will employ a hybrid work model, with fewer people in the office and more full-time remote employees. As a major portion of the workforce develops the skills and preference for effective remote work, they will come to expect a work-fromanywhere strategy from their company rather than an exception-driven remote-work policy. Expect this to reshape talent acquisition, moving right into talent poaching, as the most desirable workers seek location agnostic work opportunities.
33% of data breaches in 2021 will be caused by insider incidents, up from 25% in 2020
Remote work drives uptick in insider threats. Three major factors that will produce an uptick in insider threats:
1) the rapid push of users, including some outside of companies’ typical security controls, to remote work as a result of the COVID-19 pandemic;
2) employees’ job insecurity;
3) the increased ease of moving stolen company data.
Combined, these will produce an increase of 8 percentage points in insider incidents, from 25% in 2020 to 33% in 2021
30% of firms will increase spend on cloud, security and risk, networks and mobility
Leading CIOs will embrace cloud-first and platform strategies for speed and adaptiveness, eschewing stovepipes for end-to-end solutions. Interviews with leading CIOs found that they are collaborating more across organizations, objectives, and budgets, extending IT-business partnerships into enterpriselevel shared accountability. They will also invest aggressively in employees, breaking down old ideals and resolving resistance within the organization.
CIOs focused on employee experience (EX) will help their firms attract, develop, and retain talent that can provide competitive advantage in a critical year.
CIOs who are slow or unable to adapt will have at least two problems on their hands:
1) massive attrition
2) getting mired in short-term fixes, like tech modernization, simplification, and consolidation, that achieve only digital sameness through peer-comparison strategies by the end of 2021
The global public cloud infrastructure market will grow 35% in 2021
The impact of the global pandemic reinforced the tremendous value and necessity of cloud computing to the world’s economy and workforce. Without cloud apps, tools, and services, businesses could not have sent millions of workers home, maintained global supply chains, or shifted entire industry business models in a matter of weeks.
The changes brought about by COVID-19 forced companies to prioritize speed and customer experience over cost savings and efficiency — and they flocked to public cloud services faster than ever. It is predicted that the global public cloud infrastructure market will grow 35% to $120 billion in 2021.
Regulatory and legal activity related to employee privacy infringements will double
Forrester predicts that in 2021, regulatory and legal activity regarding employee privacy will double. While European regulators are already enforcing privacy rules to protect employees’ personal data, countries such as Brazil, India, and Thailand will soon do the same. Companies must take a “privacy by design” approach when handling employee personal data. Doing this entails identifying and following all relevant requirements, including and beyond privacy; assessing specific privacy and ethical risks; and communicating transparently with employees.
The Cybersecurity and Infrastructure Security Agency (CISA) is leading a ransomware awareness campaign, Reduce the Risk of Ransomware, with information and resources for organizations and individuals to use.
During Ransomware awareness campaign, CISA emphasizes nine key messages that promote smart cyber behaviors or actions that individuals and organizations should implement to help prevent and mitigate ransomware attacks.
1. Keep Calm and Patch On – Patching is essential for preventive maintenance that keeps machines up-to-date, stable, safe, and secure against malware and other cyber threats.
2. Backing Up Is Your Best Bet – It is critical to set up offline, encrypted backups of data and to regularly test your backups. The more you automate your backup system, the more frequently you can back up your data.
3. Suspect Deceit? Hit Delete – If an email looks suspicious, do not compromise your personal or professional information by responding or opening attachments. Delete junk email messages without opening them.
4. Always Authenticate – Implement multifactor authentication (MFA) to prevent data breaches and cyber-attacks. This includes a strong password and at least one other method of authentication.
5. Prepare and Practice Your Plan – Create, maintain, and exercise a basic cyber incident response plan and associated communications plan that includes response and notification procedures for a ransomware incident.
6. Your Data Will Be Fine If It’s Stored Offline – Local backups, stored on hard drives or media, provide a sense of security in case any issues occur. Keep your backup media in a safe and physically remote environment.
7. Secure Your Server Message Block (SMB) – SMB vulnerabilities allow their payloads to spread laterally through connected systems like a worm. CISA recommends all IT professionals disable their SMB protocols to prevent ransomware and other malware attacks.
8. Paying Ransoms Doesn't Pay Off – The U.S. government recommends against paying any ransom to cyber-crime organizations or malicious cyber actors. Paying a ransom only funds cybercriminals, and there is no guarantee that you will recover your data if you do pay.
9. Ransomware Rebuild and Recovery Recommendations – Identify the systems and accounts involved in the initial data breach and conduct an examination of existing detection or prevention systems. Once the environment is fully cleaned and rebuilt, issue password resets for all affected systems and address any associated vulnerabilities and gaps in security or visibility.
CISA Resource: Reduce the Risk of Ransomware Awareness Campaign
One of the key elements for effective Threat Mitigation through appropriate Control Implementation is to correctly identify the Risk associated, without which the ability to Detect & Protect Security Gaps, Operating Costs and Strategic Roadmaps would get affected.
Checkout the Python Scantron API client for interacting with the Scantron API and driving automated workflows.
More details: https://github.com/rackerlabs/scantron
Today, Microsoft has taken additional steps to further support their customers who are still vulnerable and have not yet implemented the complete security update. With the latest security intelligence update, Microsoft Defender Antivirus and System Center Endpoint Protection will automatically mitigate CVE-2021-26855 on any vulnerable Exchange Server on which it is deployed. Customers do not need to take action beyond ensuring they have installed the latest security intelligence update (build 1.333.747.0 or newer), if they do not already have automatic updates turned on.
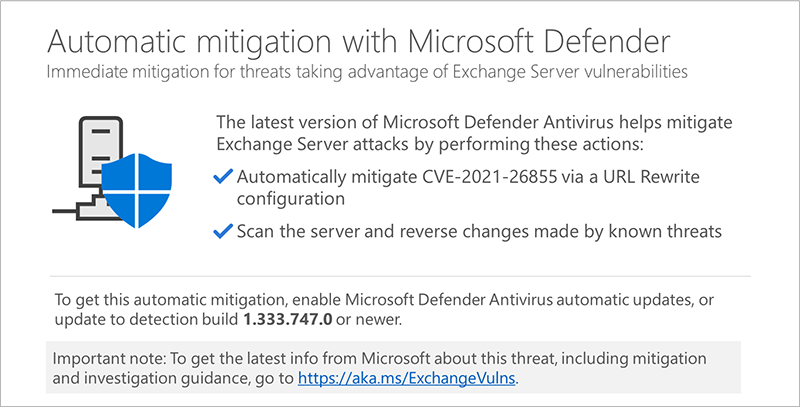
The Exchange security update is still the most comprehensive way to protect your servers from these attacks and others fixed in earlier releases. This interim mitigation is designed to help protect customers while they take the time to implement the latest Exchange Cumulative Update for their version of Exchange.
More details here: https://www.microsoft.com/security/blog/2021/03/18/automatic-on-premises-exchange-server-mitigation-now-in-microsoft-defender-antivirus/
As the Security threat landscape, these days, changes and evolves on such a frequent basis, it has becomes imperative to stay vigilant of the Cyber criminals and their ever changing tactics and techniques in a continuous manner. Organizations traditionally invest on keeping themselves updated/vigilant about the latest developments in the threat landscape through the adoption of Cyber Threat Intelligence (CTI) capabilities. Various information sources such as Blog posts, Tweets, Research papers, White papers, Vendor reports, Threat reports, Organization’s own Telemetry etc. are processed, analyzed using advance Machine Learning (ML) and Artificial Intelligence (AI) algorithms to generate actionable intelligence such as indicators of compromise (IOC), malware source IP addresses, domain names, email addresses, malicious file hashes etc. for proactive defense against these threat vectors. This traditional CTI approach to stay vigilant, however, is a very daunting task as it definitely has some limitations and challenges, such as –
·
Apart from the ML
and AI, it also requires a lot of manual time and effort to read and analyze Research
papers, White papers, Vendor reports, Threat reports etc. to understand the
context and generate actionable intelligence.
·
Validating the actionable
intelligence is also time and effort intensive and monotonous work, which
eventually could have significant false positives for Blue Teams and Operations
Teams.
·
Actionable
intelligence could be susceptible to changes as aspects like indicators of compromise
(IOC), malware source IP addresses, domain names, email addresses, malicious
file hashes etc. could change, rendering the proactive detection rules useless.
·
A major portion
of the CTI generated may not be relevant for the Organization’s technology
footprint.
·
A huge contribution
towards getting relevant real time threat intelligence is subscription based
and eventually it has cost implications.
In light of the above
limitations/challenges and David Bianco's Pyramid of Pain, adoption of MITRE ATT&CK Framework provides a structured
way to describe adversary Tactics, Techniques and Procedures (TTP) and behavior
and allows a more widespread alignment across multiple Cyber Security domains
viz. Threat Intelligence & Threat Hunting, Red Teaming, Risk Management, Intrusion
Detection & Response, Security Engineering, 3rd Party/Vendor Risk
Assessment etc.
The Pyramid of Pain – “shows the relationship between the
types of indicators you might use to detect an adversary's activities and how
much pain it will cause them when you are able to deny those indicators to them”.
This means, it is very easy for an adversary to change the malware source IP
addresses, domain names, email addresses, malicious file hashes etc. to make rendering
the proactive detection rules useless; however, it is very difficult for an
adversary to change the tactics, techniques and procedures.
This is a brief & conceptual map of all the major focus areas of Cyber Security. This is more of a quick snapshot of the Cyber Security Domains that requires proper planning and strategies carved out to improve an Organization's overall Security posture.